Attacks tend to find the common denominator. What is the most common shared resource between the most devices under attack. For a long time this has been the Microsoft Windows operating system. The reason it remains the mainstay of malware is that it is ubiquitous. It is everywhere. If you attack Windows, you are attacking most of the desktop and laptop computers in the world. But not the mobiles.
Mobile devices come in a variety of operating systems. Several flavors of Linux, iOS, Android, (again in several major flavors) and even Windows 8.1 and Windows RT. There is no one Operating system that defines the product category. In fact, no exact system carries even a quarter of the devices, and a great share of those systems exist only in walled gardens provided by Apple or Blackberry. So the operating system is not the attack point of choice at this time.
Now if you are not attacking the individual client systems, you are no longer talking about malware. Not as we know it today. Instead, there is one thing that ties together all of the world’s mobile computing devices, and that one thing is 802.11 Wireless networking, commonly known as WiFi.
Sure your phone has other networking options, but even a machine that allows for cellular data communications will default out to WiFi, for a connection both faster and lower cost. Many devices will default auto-connect to any available WiFi network. There’s your Achilles’s heel. There is the weakness in mobile data communications. WiFi can be subverted, it can be infiltrated, it can even be stolen.
Anyone can pretend to be the network you are connecting with, from your local coffee shop to the airport lounge. Pretending to be a trusted connection is called an EVIL TWIN ATTACK.
With a little more skill, the would be criminal could listen in on an existing wireless connection using an antenna and some pre written software. As long as the data is not encrypted, it is all too easy to eavesdrop. The tools to accomplish this are available all over the internet, and for free.
Then it is possible that you are connecting with a known and trusted source, in your library or airport or coffee place, but that a bad guy has infiltrated that source with some kind of injection attack and thus pwns all the traffic that goes through it. This is common as well.
This leaves your mobile device exposed and insecure, without ever being touched by a virus or Trojan or malware of any kind. You see, there are lots of problems at the client end of things, but many problems in other locations as well. Yesterday’s problem is not the same as today’s, and that is not the same as tomorrow’s. What can you do?
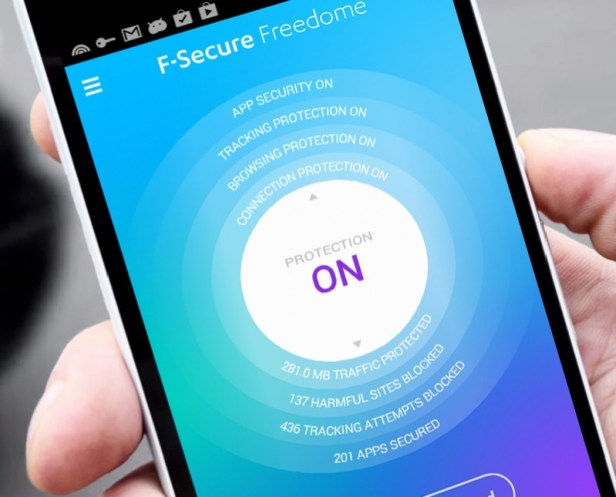
Every now and then I am very happy to represent a company, and today is that day. My employer, F-secure, has come up with a solution that is elegant and thorough for the mobile user, it is called FREEDOME.
FREEDOME encrypts all the traffic to and from your device, blocks you from bad websites and stops malware actions in the cloud, before they ever get to your i OS or Android based device. It’s pretty inexpensive, less than thirty dollars per year and it will block thousands of attempts to track your phone every week. With FREEDOME your device, phone or tablet is anonymous and secret. You appear to come from some other state, or some other country. Your communications are stripped of your identity and of your location. This has a number of benefits.
You can get a two month free trial of FREEDOME at this address:
Write back and let me know what you think!
Persevere,
David Perry

I can’t read the text on the inner circle in the graphic – insufficient contrast for my aging eyes …
LikeLike
Let me see if I can find a better graphic…
LikeLike