What is it exactly that we are protecting you from? This has changed a great deal over time. The very nature of computing has changed a lot over the same time. At the very beginning, from my perspective, we were protecting you from viruses.
Now why would you want your computer protected from Viruses? The common wisdom about this was that viruses would destroy your computer, or at least your data, and that’s why you wanted protection. This would be in about 1990. Viruses did not then, and do not now destroy your computer. There were a vanishingly small number of them that pretty much made your computer unusable, mostly by erasing your flash ROM BIOS, but there really isn’t any percentage for anyone in destroying your computer. For one thing, it kills off the ability of that computer to serve as a source of infection for anybody else.
And these days most malware (it’s all malware, even viruses) is written strictly for profit, and making it replicate itself (as viruses must to be called viruses) or spread themselves from computer to computer (which would make them worms, which are a subset of viruses, because you cannot spread yourself from system to system without making copies of yourself). So instead of those old versions, (mostly written by computer programming students in search of glory) of malware, most of today’s malware is non replicating. This makes it harder for antivirus companies (who really should be called antimalware companies because they have all tracked all manner of malware right from the very start) to find a sample that they could use to produce a detection.
Because of this, and because of a major misunderstanding about this, we frequently find ourselves hearing that “Antivirus is dead”. In fact, a major player over at Symantec corporation said that just last year, and immediately ended up working at General Motors.
Confused yet? Well, many people are. In this industry we only have products that are still called antivirus is because most people go look for that on the shelf. Every year some manufacturer wants to promote some bigger and better new product and declares that antivirus is dead. We all get a laugh out of this. Dead and buried for years, the truth be told.
Are there still viruses? Yes there are, many hundreds of thousands of them. Are there still new viruses? Yes there are, every minute of every day! Do antivirus and antimalware agents (program) still work the way as they did in the past? No. Not at all.
That original engine, where pattern files are downloaded each day is still needed. (although that download happens many times each day) Although most malware is not self replicating, most of the known items these days are strictly front-end. I have always liked to call them HOOKWARE, because they are the initial hook that first catches a system and then downloads the more advanced workings to each infected systems. Sometimes it is a bot (which taken together with other such infected machines is called a botnet.) Sometimes it is analysis software, used to determine how best to utilize a system once it is infected. Sometimes it is there to steal a password, or to steal a credit card number, or to learn more about the computer and the user, seeking to resell the data at a later date, or insert advertising into our computer use. We might call that SPYWARE or ADWARE.
There is also the presence of Ad-supported software on your system that is completely legal and does just what the spyware or adware would do but it is legal, you agreed to it. You might also belong to social networking sites that constantly keep data about you and resell it, or use search engines that do the same. This is the current most successful and lucrative computer business and it’s quite legal. We don’t even try to block it, because we all agreed to it.
 I would recall to you the words of the dean of science fiction, the late Robert Anson Heinlein, who once said TANSTAAFL, or, “There ain’t no such thing as a free lunch!” Our own Mikko Hypponen has added to this: There is no such thing as a free browser. There is no such thing as a free search engine. There is no such thing as a free app. Beware of geeks bearing gifts, and start paying attention, this can lead to no good in the long run.
I would recall to you the words of the dean of science fiction, the late Robert Anson Heinlein, who once said TANSTAAFL, or, “There ain’t no such thing as a free lunch!” Our own Mikko Hypponen has added to this: There is no such thing as a free browser. There is no such thing as a free search engine. There is no such thing as a free app. Beware of geeks bearing gifts, and start paying attention, this can lead to no good in the long run.
Almost every package on the market is more than mere string detection. Most contain a ‘rule of thumb’ engine (frequently called a heuristics engine) that looks for properties that might be best described as acting malware like. These rules are constantly updated all the time and are matched to the most common characteristics of the day.
Almost every package has a reputation service built in. This blocks malicious files and files that come from malicious websites and emails by both an updated database of known bad locations and a series of heuristic rules of their own. A very good rule of thumb for a reputation service on websites would be to block all domains on their first hour or first day of existence, or websites that look very similar to a popular website but with only one character different.
Almost every package is doing whitelisting. This is where, in addition to looking for files that are known to be bad (which is known as blacklisting) one creates a list of the known good files that are on a given system. This is more difficult to do, as it doesn’t stand still to be identified. Any time you go online you might be adding browser helper objects or extensions to your browser, and even apps as stable as the popular Microsoft Office components require frequent updating.
Also, most contemporary Applications and Utilities (programs) are not a single file, but a huge constellation of programs, libraries, drivers, data files, run time applications and other files. Just to catalog these is a full time job. Even when this is done perfectly, few people like to run a very tightly whitelisted system. In fact, most users demand to be run in administrator mode all the time, such that the OS’s own first line of defense against rogue code is disabled.
Behavior Blocking is when the actions one might find objectionable are identified and blocked from happening. Host-based Intrusion Prevention looks for patterns of behavior and states of being that violate a rule base that can be either statistical or profile based, or both. A Firewall provides clues based on the activity found on both incoming and outgoing ports. A VPN, or Virtual Private Network creates an encryption tunnel between your computer and it’s destination. A system imaging utility (also known as a ghosting utility, named for an application that currently belongs to Symantec) is something that permits recovery of an entire system whenever an infection is found.
That’s how the big players do it. Find an infection, reinstall. Frequently you can get a 100% perfect malware removal (remediation, cleaning, stripping) using only your antimalware utility but not always. We currently stand at nearly a million new pieces of malware each and every day, and hundreds of millions known to exist. So if you are an IT department, you re-image every infected system. So do many home users. I recommend that if you are a computer user, you maintain a system image library of your system at all times. This is for a number of reasons.
But we protect you from more than all of these. We protect and guard your system security, your personal privacy, and your online transactions. We do this with sophisticated and multifunction engines that are the very state of modern software development. We respect your privacy and never use our products to pry into your personal business. We are F-Secure, and we are Finnish. (I am, of course, from California, and am very proud to be associated with this fine company enough to call myself Finnish in spirit at least)–at F-Secure, I am a Fellow. All of us at F-secure are not merely employees, we are all fellows. I have never worked anywhere with more concern that every voice be heard. It is a name I wear with honor.
All of the jargon in this article I have put in bold italics in it’s first inclusion. If the definitions that I have written are not enough for you please write to me care of this blog and I will elaborate further.
By the way, F-Secure was recently named the best in the world for the fourth running year, by Virus Test (this is the largest antimalware test known and is run by Andreas Marx and his people in Magdeburg Germany, you can read about the test here)
Persevere,
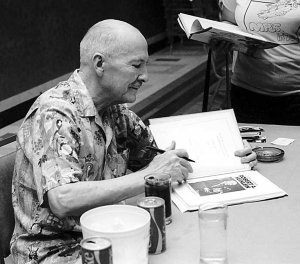
David Perry — Huntington Beach, California — March First, 2015

